Featured Posts
All Posts Sorted by Publication Date
Farewell, Memory!
July 19, 2023
Have we lost the art of remembering? With the inescapable reach of digital memory and the rise of state-led censorship — as seen in Putin's Russia — our ability to remember is in existential danger. We can say that at the visible, cultural interface of the networked image, media is now ...
JOY: Expressions of Resistance
March 1, 2023
Announcing a new literary series by Sampsonia Way Magazine! Sampsonia Way Magazine seeks writers to contribute to our newest literary series JOY: Expressions of Resistance. Inspired by the observation made by poet Toi Derricotte that “joy is an act of resistance” — we're looking for stories, essays, and poems that ...

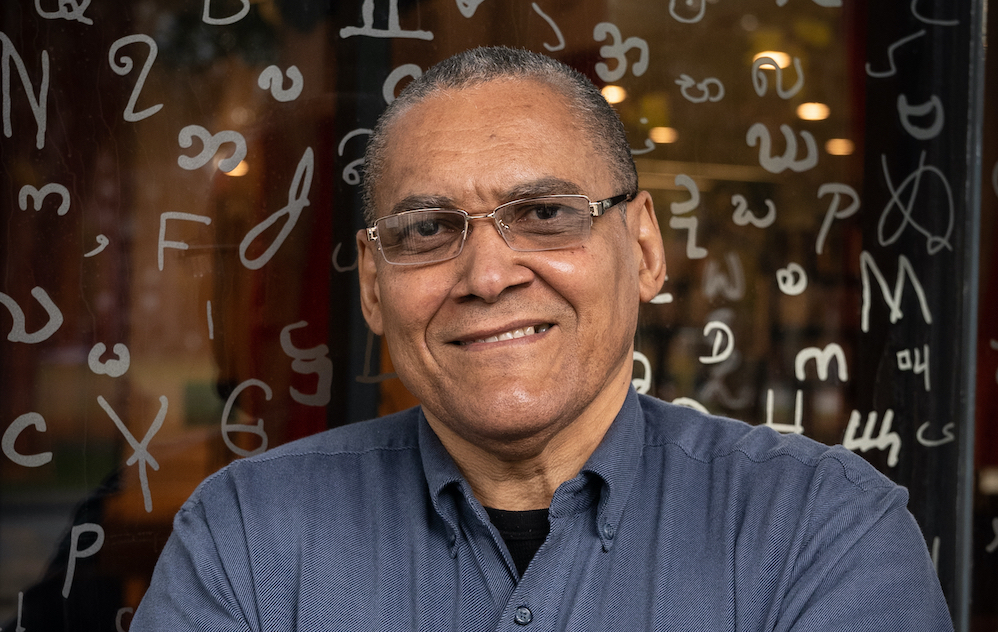
Sublime Particulars: An Interview with Emmanuel Iduma
February 23, 2023
First published on December 3, 2019, Emmanuel Iduma sat down with Cole Arthur for a wide-ranging conversation about the fluidity of form, belonging, and the importance of particularities. In September of this year, Nigerian writer, Emmanuel Iduma performed at City of Asylum’s annual Jazz Poetry Festival. He read alongside music ...

Photo Essay by Orlando Luis Pardo Lazo
January 12, 2023
Experience the world through Orlando Luis Pardo Lazo’s eyes as you explore his new photo essay encapsulating the Everyday Pandemic. Orlando Luis Pardo Lazo (born 1971) is a Cuban writer from Havana. Since 2016, he has been studying for a PhD in Comparative Literature at Washington University in Saint Louis, ...

Hospital Music by Roosha
January 10, 2023
The heart monitor blares mechanically, high frequency waves rolling through ear drums, cochlea, and finally colliding with nerves connecting to the brain, embedding a specific neural pattern in the memory forever. Behind lab coat whispers and clipboard conversations, behind the soothing therapeutic voices and informative professional reports, behind the silent, ...

Five Poems by David Dephy
December 7, 2022
STILL LIFE (April 10, 2020) Still entwined. Time passes as time does: so much behind us, a little less to go. No easy ride: peace can be vexing—what we’ve left behind as the sun dips down low. THE OTHER SIDE OF ALONE (August 2, 2021) What if we sense our ...

Three Poems by Kathleen Hellen
December 7, 2022
The incredibly complicated, solitary human being —a pandemic diptych Perhaps she is a student, worrying the degree—here, outside the service bay, beside the lot of shiny, stickered cars. No one near except this woman on a bench, who leaves as I approach, who thinks perhaps that I could kill her ...

How Dare I?
November 30, 2022
Poetry inspired by Injustice (1941), a mural by Maxo Vanka at St. Nicholas Catholic Church in Millvale, Pennsylvania. Editor's Note: The contents of this poem include graphic reference to domestic violence and sexual assault. Photo courtesy of Society to Preserve the Millvale Murals of Maxo Vanka. Photo credit: Rob Long/Clear ...

Writing on the Wall: An Interview with RaMa
November 30, 2022
The revolutionary writer from Sudan shares her story. “Like the fire that comes from a little bit of flames. We were that spark for ourselves, for our spirits, and for others.” A protester throws back a tear-gas canister that had been fired by security forces, during a march demanding an ...
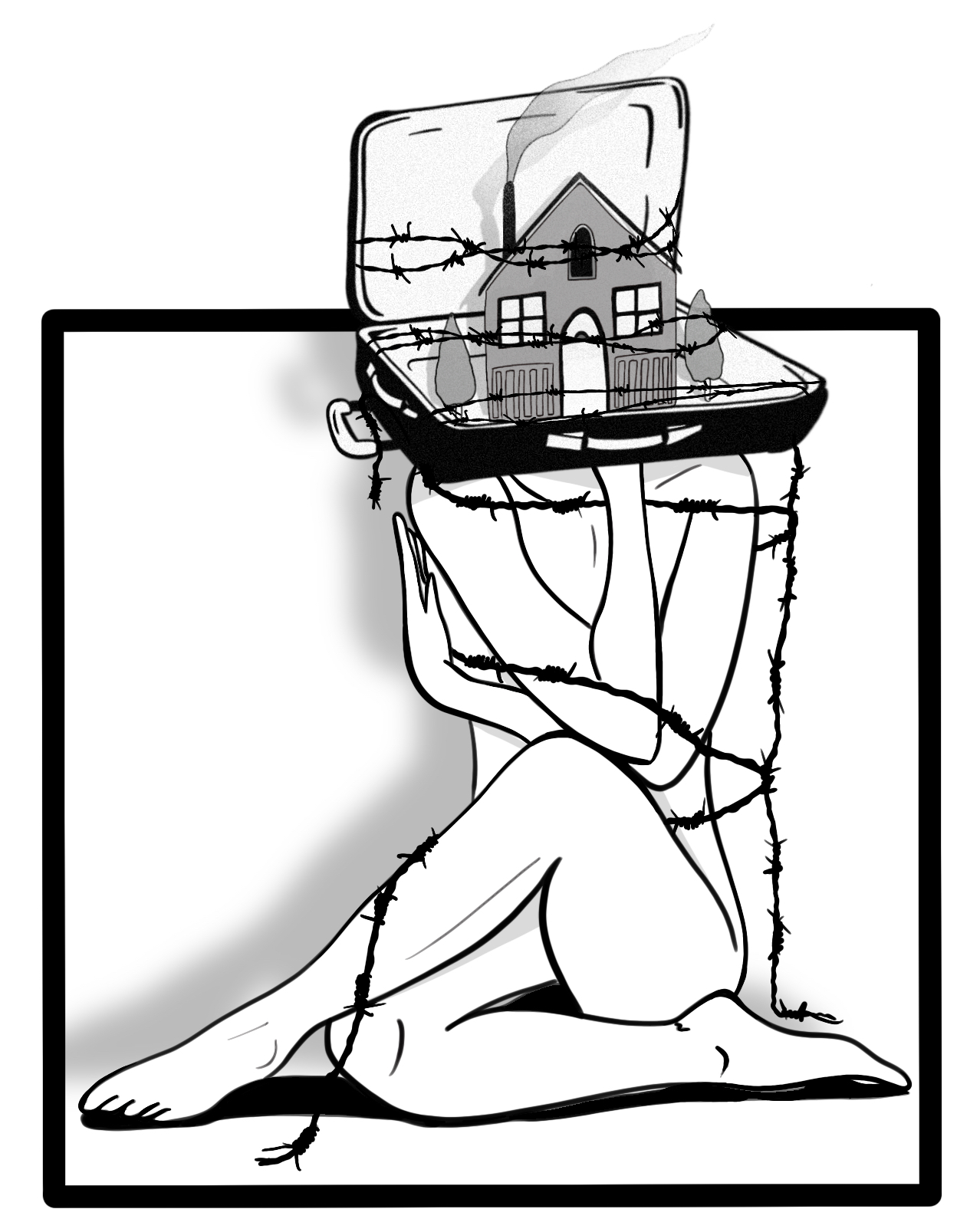
On Exiting: Fences & Wires
November 17, 2022
When we acknowledge the enclosures around our social and emotional lives, we get to reimagine a world without limits. When I lived abroad, finding asylum in places like Pittsburgh and Ithaca and in Ottawa, I was repeatedly asked how I felt about exiting my country. And I had to get ...
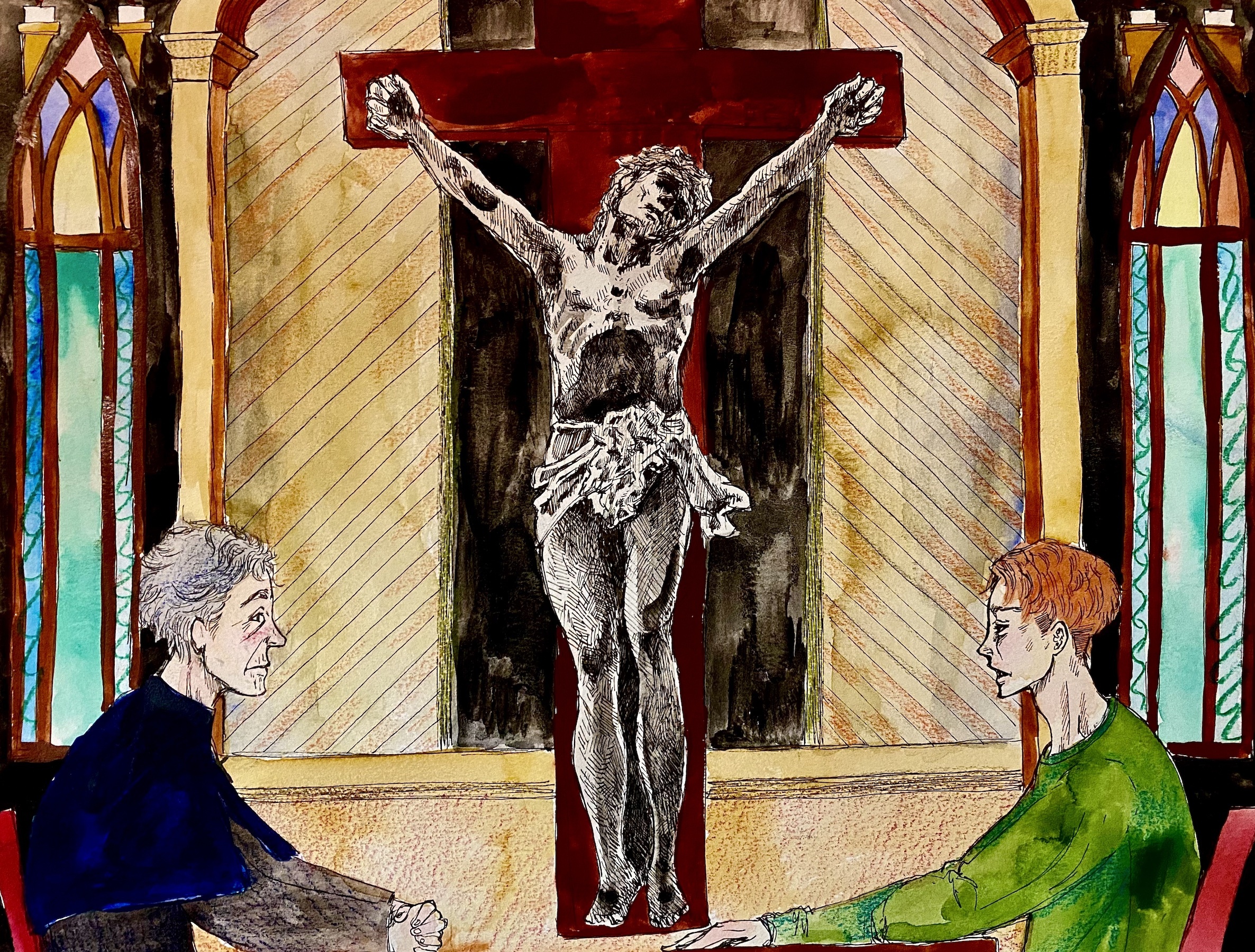
The Last Mission
November 15, 2022
Illustration by Izumi Miyazaki The eighty-year-old priest Mario waited alone for Marcus in the Windmill Church. It was the second month that the city had been shut down because of COVID, and all the churches were closed. Mario sighed loudly and looked out the window at Wigwam Street. Neither this ...
Poetry by Edward Salem
October 27, 2022
Living in the Promise of the Future I was a futurist, imagining utopian life ahead. Now here I am, I’m halfway dead. I thought scientists would defeat death. Yet here I am, ripping bread with my teeth. In forty years, we won’t need teeth. I’ll be eighty then, close to ...

Two Poems by Vyarka Kozareva
October 26, 2022
DIMENSIONS You can’t know for sure When hope really dies Or if it dies last But only feel That it defers its big plans For an undefined future. And because This future itself Is also in the future Your fingers have learned How to sift every scrap of coincidence Then ...

Symphony in Wellness: Q&A with Raychelle Heath
October 13, 2022
The multidimensional writer shares her journey of self-discovery and holistic health. Photo by Venice Williams. Raychelle Heath is a true polymath: she's a writer and a poet; a podcaster and visual artist; a translator and a teacher; and a yogi and meditation instructor. When she is not writing, you can ...
On Exiting: Assumptions, Presumptions
October 11, 2022
"Where does the home start? Where does it end?" The author explores the notion of exile, home, and (non)belongingness. Illustration by Waad Aljurayyad Nomads are free; exiles are not. So why not claim nomad/hood? For most of my life, I never pictured myself as a settled person. Instead, I romanticized ...

Three Poems by Raychelle Heath
October 11, 2022
A Beginning to a Pandemic Love Story What are the pads of fingers against the broadness of a back, how does one absorb the depth of a freckle, limp into a sea of dark curls without drowning? Hands bloom from the center of a laugh that she has finally opened ...

In a Vale of Soul Making: In Conversation with Mark Steidl and Richard St. John
October 1, 2022
The authors share how their journey began in poetry and ended in kinship. Early one September evening, Mark Steidl and Richard St. John joined Sampsonia Way for a conversation about their genre-defying piece of writing titled “Freaky Fire Guy.” In a collage of narrative writing, photography, and poetry, their essay ...
Three Poems by Anne M. Rashid
September 26, 2022
Kitty Pandemic I name cats after trees: Cedar, Sycamore, and Maple. And Star Wars: Yoda and Obi. And songs: Ziggy and Stardust. And legumes: Sweet Pea and Chickpea. This brood multiplies during the pandemic and now I am truly the crazy cat lady of the neighborhood. My own cat, Ginkgo, ...
She says this tkhine on her child’s first birthday, the world unfolding
September 14, 2022
It’s May: no fallen leaves to herd into interrogatives. Still, the wind searches, calling the names of those it’s driven out. The time between gatherings meanders on the year’s grid, a river forced northward, like a graph that shows the country repeating mistakes in two different centuries. Absence takes the ...
Entrevista a Jorge Olivera Castillo
September 12, 2022
El autor cubano comparte su recorrido como disidente. Este artículo es parte de una colaboración con la revista Pittsburgh Latino Magazine. Jorge Olivera Castillo es un poeta, escritor, editor de televisión, reportero y compositor cubano. En Cuba, fue conocido como disidente y defensor ferviente por la libertad de expresión provocando ...

